HIPAA and Electronic Health Records: All You Need to Know About Compliance

Healthcare is digitizing quickly, and the COVID-19 pandemic only fastened this process.
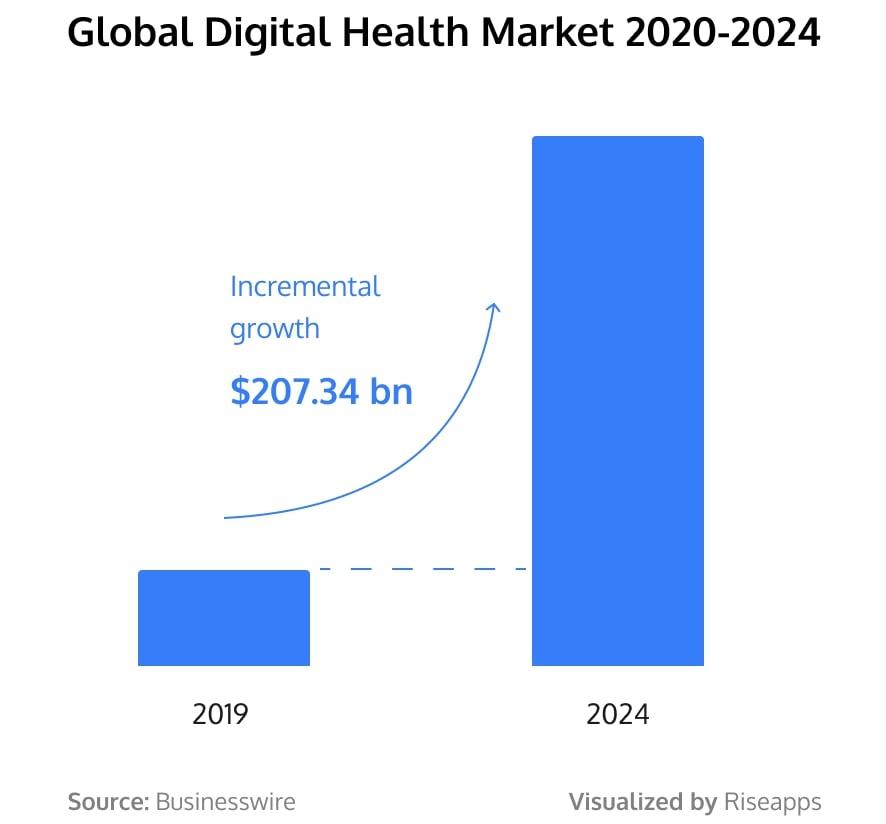
The global digital health market is expected to grow by USD 207.34 billion during 2020-2024, at a formidable CAGR of over 20% during the forecast period.
As doctors get rid of paper charts, EHR/EMR systems are becoming even more popular. According to CDC, almost 86% of office-based physicians in the US are using them. Along with that, healthcare apps are often integrated with EHRs and EMRs to improve the level of medical services. So the question of HIPAA regulations on electronic medical records is becoming more and more vital.
If you are building an EMR/EHR tool or want to connect it to your software, wondering how to stay HIPAA compliant, you are on the right track.
At Riseapps, we have a wealth of experience in building secure healthcare tools that store medical data. In this article, we’ll share with you some guidelines on how to protect patient health information (PHI) and save yourself from devastating penalties and lawsuits. Read on.
Difference between EMR and EHR systems
For those who just started exploring the topic, let’s share some basics. Is there actually a difference between EMR and EHR systems?
Indeed, the names of the systems are often used interchangeably. E.g. a popular software review website Capterra doesn’t even offer a separate page for EHR software. It’s all listed in the EMR software section. However, the difference between the two systems is quite significant.
The key to understanding the distinction lies in the gap between the words “medical” and “health”. The latter covers a lot more territory, so EHRs go a lot further than EMRs, as explained in the official article written by the ONC experts.
In short, here’s the main difference:
In EHRs, data can be created and managed by authorized clinicians and medical staff across more than one healthcare organization. EMR systems are supposed to be used within one healthcare organization only. The information in EMRs doesn’t travel easily out of the practice.
At the same time, since the functionality of EHR and EMR systems is similar, sometimes it seems reasonable for the terms to be mutually substituted.
Basically, EHRs provide more benefits to a hospital, physician, or health +care organization than EMRs. It is a good idea to keep that in mind if you are choosing between the two.
Another question to consider is about HIPAA laws and EHR.
How Does HIPAA Affect Electronic Medical Records?
HIPAA and electronic medical records are inextricably linked. Since EHR/EMR data is considered patient health information, these kinds of records are under federal protection. The law that guards and preserves PHI is HIPAA – the Health Insurance Portability and Accountability Act.
Adopted in 1996, this law has been updated and expanded with the Health Information Technology for Economic and Clinical Health Act of 2009. It applies to “covered entities” and “business associates”. ”You can explore the HIPAA act yourself here, but some experts fairly refer to it as “the 800-pound gorilla in the room.” It might not be easy to comply with all HIPAA requirements for electronic medical records. So, if you wonder how to make your tool safe, it’s a good idea to turn to experts, apart from studying the subject yourself.
In a nutshell, HIPAA has two components: privacy and security.
Privacy Rule is designed to set the standards and processes for access to PHI. It gives patients rights concerning their health information and sets limits on how their health information, stored in an EMR/EHR system, can be used and shared with others. You can read more about the Privacy Rule here.
Security Rule sets rules for how patients’ health information must be kept secure. It’s filled with administrative, technical, and physical safeguards you can apply if you build an EMR/EHR tool. More information about restrictions in Security Rule can be found here.
Apart from HIPAA Privacy and Security Rules for electronic health records, there’s a Breach Notification Rule. It requires HIPAA covered entities and business associates to provide notifications following a breach of unsecured protected health information. The law states that if there’s a breach of health information protected under HIPAA, it needs to be reported to the HHS. When a breach includes 500 or more records, it’s tracked in a public HHS database.
To minimize the risks of breaches when building an EMR/EHR tool, turn to a trusted healthcare software development company like Riseapps. We’ll make sure to successfully implement all the Technical Safeguards standards.
To wrap it up, when it comes to building EHR or EMR tool, implementation of HIPAA rules is crucial.
Electronic Medical Records and HIPAA Violations
In 2019, there was a high-impact case in the digital healthcare world. Medical Informatics, an EMR сompany, had to pay a $900,000 settlement for a health data breach impacting 3.5 million patients in 2015. Officials discovered a “sophisticated cyberattack” on the servers of the organization that allowed hackers access to the PHI of patients, including clinical data and social security numbers. This particular case featuring EHR and HIPAA violations attracted unprecedented attention, but it wasn’t a random event.
As of 2020, 393 protected health information breach incidents were reported to HHS in the past 12 months. They included malicious email hacking, unauthorized access to EHRs and medical records, as well as downloading PHI on an unauthorized computer or device.
The question is how to avoid these grave mishaps, as HIPAA concerns with electronic medical records could be rather diverse. Needless to say, the key is to ensure strict EMR (or EHR) compliance with HIPAA and appropriate security protections for PHI.
When lawyers analyze various breaches, they often stress the importance of сonducting risk assessments, which are a clear requirement under HIPAA. This kind of checks must be completed in a necessary manner, the results should be reviewed and issues addressed.
Now, how do we take care of privacy and security, when designing and developing an EMR/EHR tool?
HIPAA Privacy and Security Rules and Requirements for Electronic Health Records
Sidenote: this article is written for informational purposes and can’t be used as legal advice. We suggest you consult your lawyer about complying with HIPAA regulations and get an expert opinion on your particular case from a qualified software engineering company.
Since it’s a brief guide, we’ll list just 3 main requirements for HIPAA compliant electronic medical records (or electronic health records).
These common measures can be built into the EMR/EHR systems to ensure Privacy and Security rules.
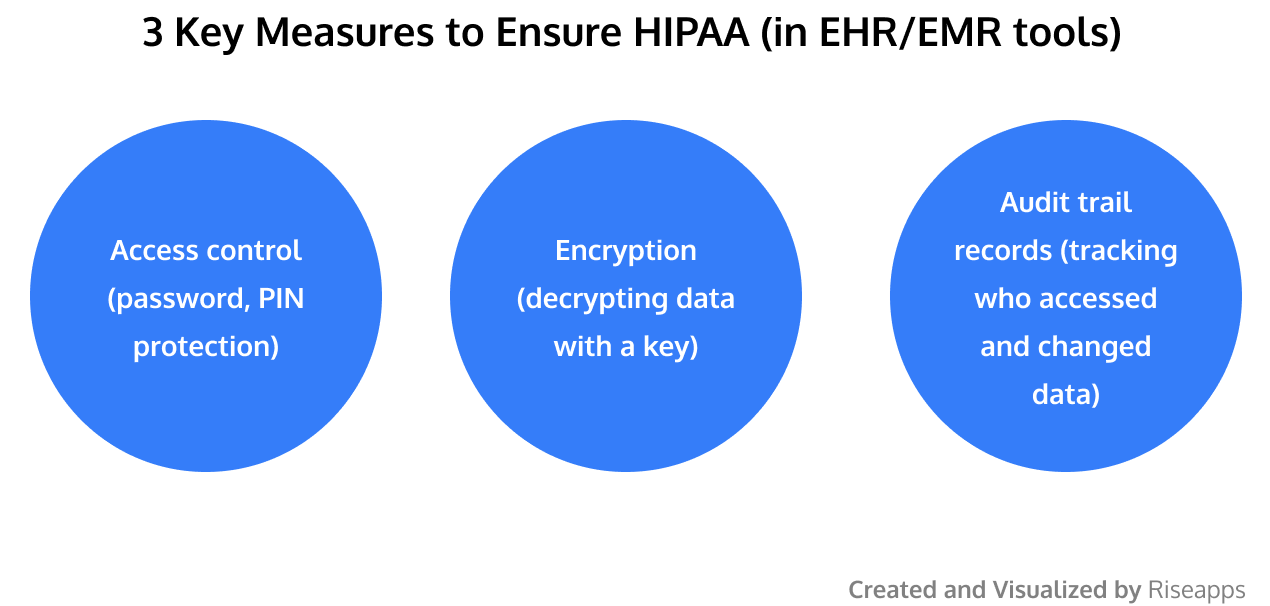
- First, it’s all about “Access control”. Tools like passwords and PINs help limit access to patient health information to authorized individuals. Password policies usually address the strength of passwords, the frequency for changing them, and not disclosing or sharing passwords.
A covered entity may also require something that individuals possess, such as a token, or something unique to the individual such as a biometric. Examples of biometrics include fingerprints, facial, voice or iris patterns.The important specification associated with the access controls standard is automatic logoff.According to HIPAA, covered entities must follow “electronic procedures that terminate an electronic session after a predetermined time of inactivity.” By implementing the automatic logoff into your healthcare tool, you help healthcare providers prevent unauthorized users from accessing EPHI on a workstation if it is left unattended for some time.You can implement configuration settings for automatic logoff. As an option, your healthcare app might activate an operating system screen saver that is password protected after a period of system inactivity. In either case, the information that was displayed on the screen should no longer be accessible to users who don’t have official approval or permission for that. - Second, “encrypting” your stored information is of the essence.Encryption is a way of converting an initial message of usual text into encoded text. The data is encrypted by means of an algorithm (i.g. formula or type of procedure). In such a way, PHI stored in the tool cannot be read or understood except by those using a system that can decrypt it with a designated “key.”The goal of encryption is to protect EPHI from being accessed and viewed by unauthorized users. So when building an EMR/EHR it is important to ask a question what encryption and decryption mechanisms are reasonable to implement.
- Last, but not the least is an “audit trail” feature, which records who accessed your information, what changes were made and when.
Usually, a guideline on audit trail features contains
- Automated information captured at the time when a record is created, altered, or deleted
- A record of the specific user modifying or just accessing the information
- Immutable storage security, which makes any alteration of the audit trail by administrators or users impossible
In a nutshell, audit reports are useful for recording and examining information system activity, especially when determining if a security violation occurred.
Note, however, that Security Rule does not identify data that must be gathered by the audit controls or how often the audit reports should be reviewed. It’s a covered entity that should consider its risk analysis and organizational factors, such as current technical infrastructure, hardware and software security capabilities, to determine reasonable audit controls for information systems that contain or use EPHI.
To learn more about measures that help ensure the privacy and security of your HIPAA compliant tool, feel free to contact us.
Our Experience
At Riseapps, we have first-hand experience in building HIPAA compliant tools that document the patient’s health information.
Among many cases in building HIPAA compliant healthcare apps, let’s mention Kego.

It’s the on-demand service – an ‘urgent care clinic’ – where patients can see a doctor via video conference. The web and mobile apps allow patients to book appointments, chat with experts, and store their medical data in digital form. Riseapps built Kego apps for iOS, Android and web, providing design, software development, QA, and other services. For messaging and videoconferencing, we used Twilio and its SDK.
Read Also: HIPAA Compliant Chat SDKs for Messaging and Video Conferencing
So how did we ensure privacy and security of the tool? With this question, we turned to Dmytro, a senior iOS developer with 15-year experience in software engineering, who was in charge of the project. Here’s what he mentioned:
- When building the app for the iOS platform, we used a Keychain framework that allows storing encrypted PHI data.
- Speaking of PHI transmission, we used HTTPS – communication protocol, encrypting data with SSL/TLS.
- We implemented automatic logoff when the app is left unattended for a long period of time. This serves as an effective way to prevent unauthorized users from accessing PHI.
Going forward, we are proud to have built a safe and solid HIPAA-compliant app allowing people to get quick medical help from home.
Conclusion
In this article, we looked at HIPAA and EMR (EHR), exploring how to make these records secure.
We noted the difference between the electronic health and medical records, which lies in the fact that EHRs are more extensive, while health data in EMRs is limited to a single provider. However, since the functionality of EHR and EMR systems is similar, the names are often used interchangeably.
Under HIPAA regulation, EHR/EMR data is considered PHI. Therefore, tools that store the records must be HIPAA compliant to protect clients’ healthcare data from security incidents, which can cost up to hundreds of thousand dollars. So HIPAA and EHR implementation go hand in hand.
A few possible measures that can be built into your tool to ensure HIPAA and ehr compliance include: “access control” tools like passwords and PIN numbers, “encrypting” your stored information, and the “audit trail” feature, which records who accessed your information, what changes were made and when.
Basically, the topic of electronic medical records and HIPAA compliance is broad and diverse. This is a brief guide, so if you have more questions about HIPAA and electronic health records, feel free to get in touch with us.
And in case you’re on the way to building a solid EMR/EHR tool, or integrate it with your app, we are ready to help. Riseapps is a healthcare software development company offering custom app development at a reasonable cost. If it sounds appealing, just ping us with a message, we’ll get back to you in no time.
Contact Us






